
The 2018 Marriott–Starwood Data Breach
In late 2018, Marriott International revealed a massive data


In late 2018, Marriott International revealed a massive data
For decades, antivirus software stood as the gatekeeper of

Cybercrime has grown exponentially in recent years, with cyber

— And Why Your Business Needs a Cybersecurity Partner




Understanding everything from infiltration to prevention In recent times,


Unveiling the Complexities of IoT Security Interconnected ecosystems

How to protect yourself against the timeless cyberattack?

The security researcher and investigators have found an open

Introduction: Spear phishing has evolved into a popular
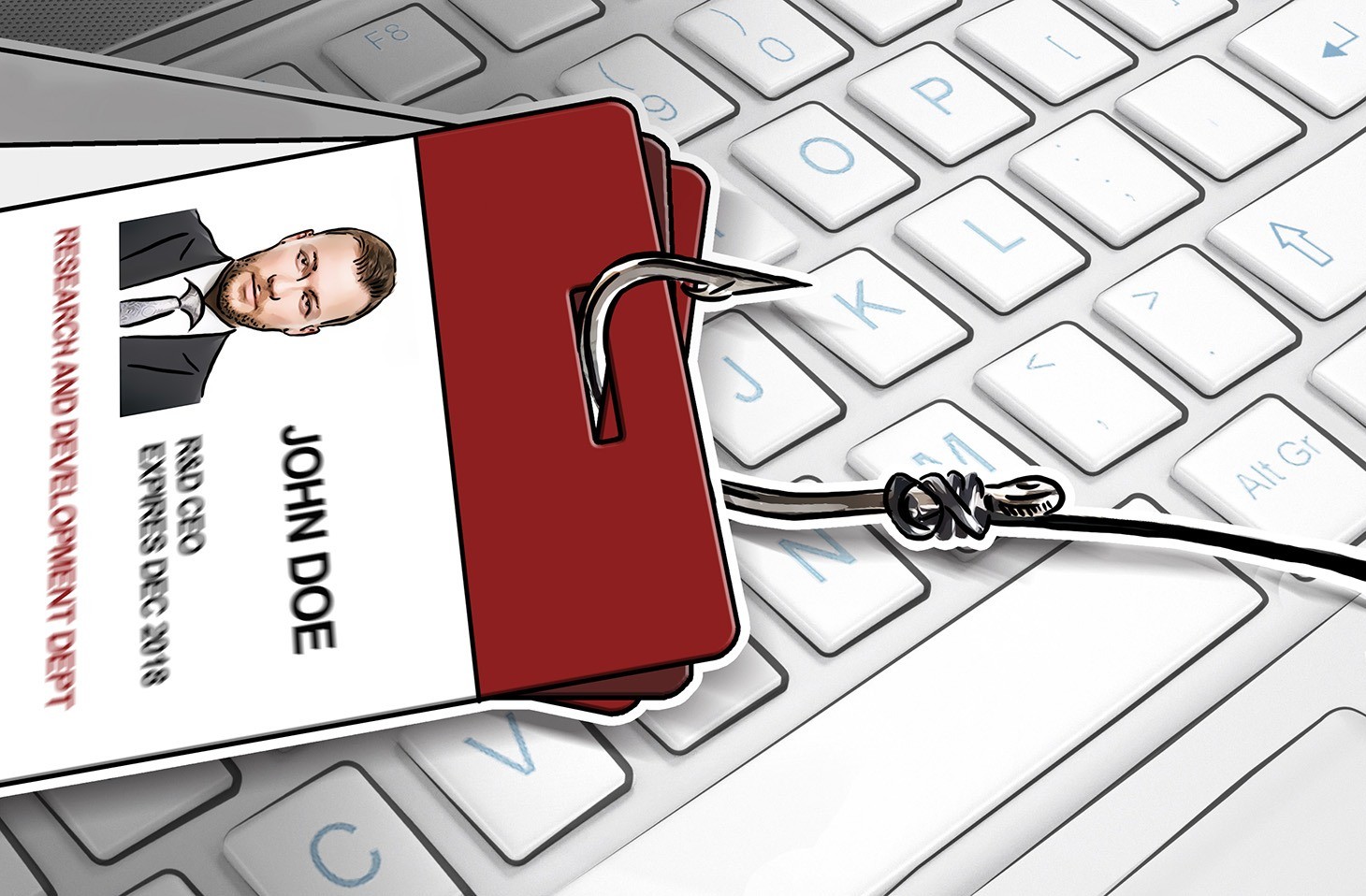
Introduction: Spear phishing has become a widespread cyber
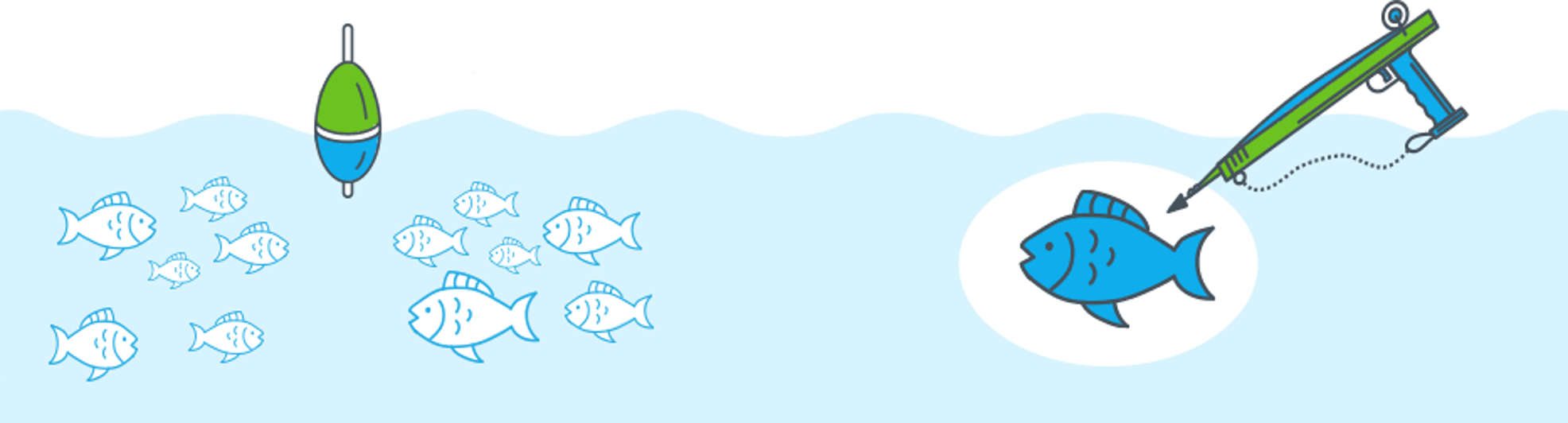
Introduction: Phishing and spear phishing have the same

Introduction: Spear phishing has developed as a critical


Introduction: Spear phishing may have a more
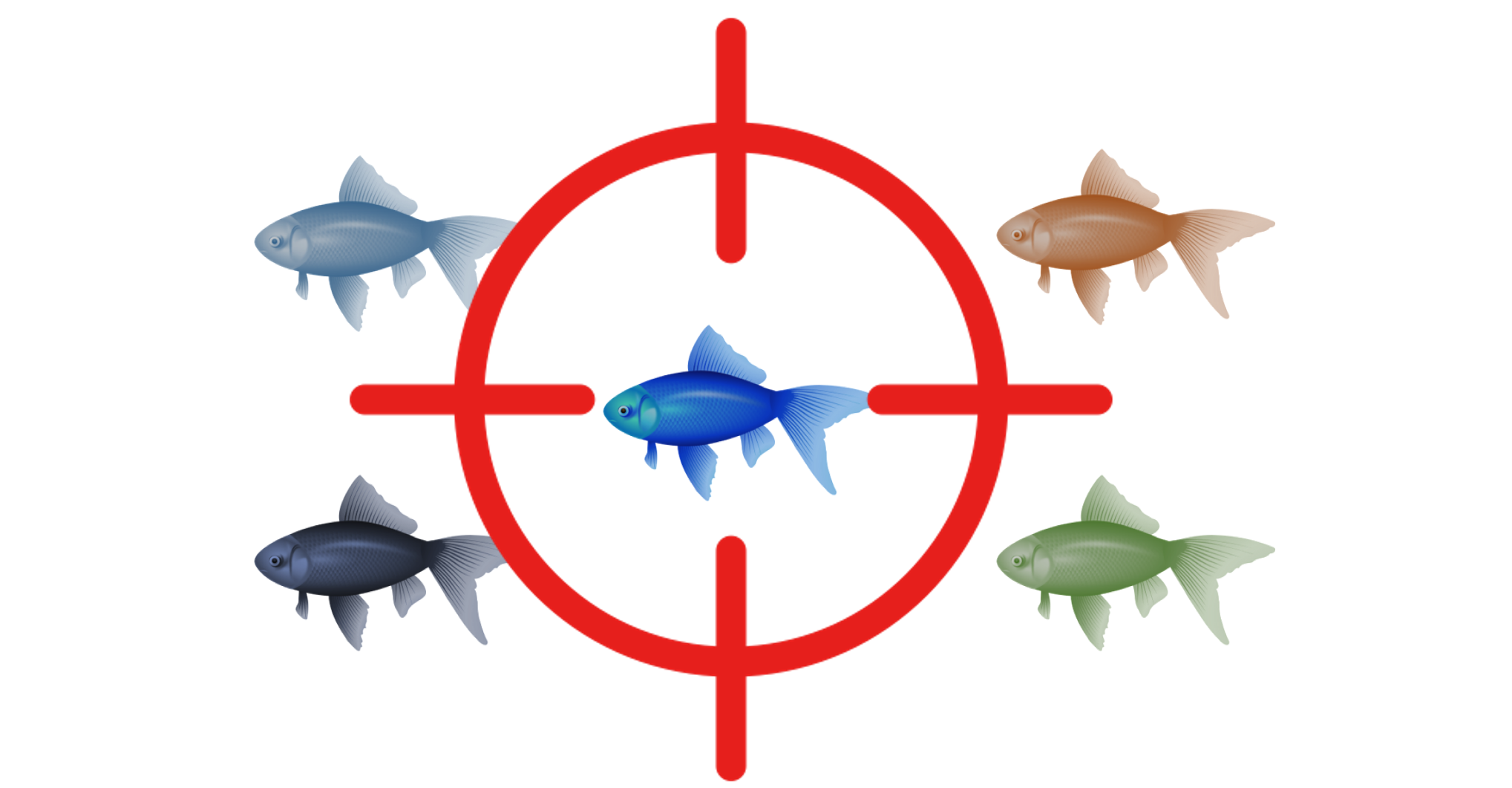
Introduction: A spear-phishing attack frequently consists of multiple
© 2025 ParadigmIT Cybersecurity. All Rights Reserved.