Introduction:
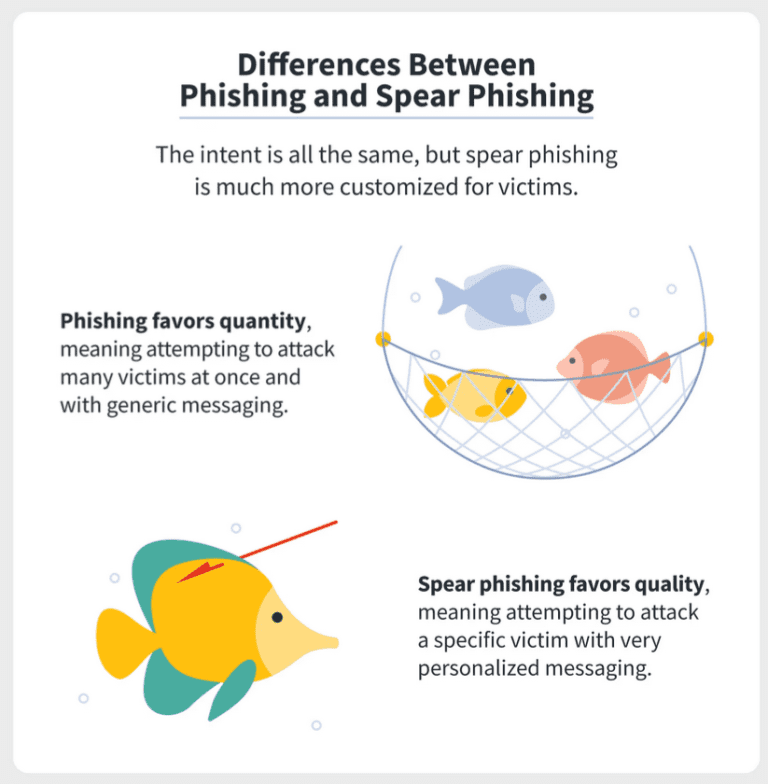
Phishing and spear phishing have the same goal: to deceive people into exposing confidential details such as usernames and passwords account numbers, or sensitive data. However, there are some similarities between spear phishing and phishing
The difference between phishing and spear phishing are:
Phishing:
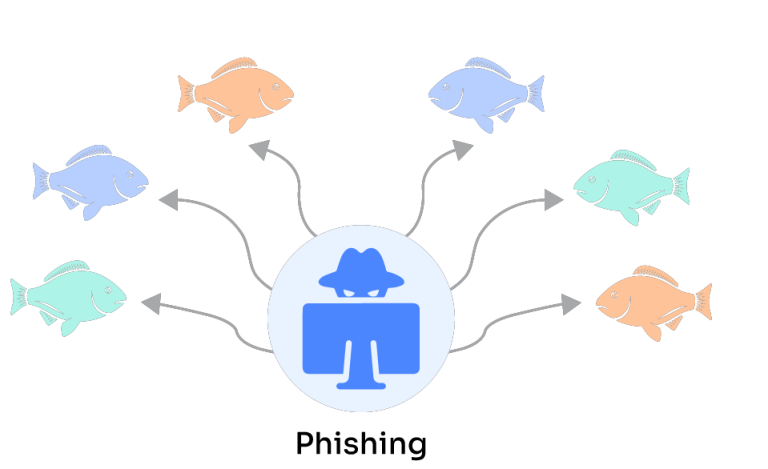
Phishing favors quantity, meaning attempting to attack many victims at once and with generic messaging.

- Attackers pretend to be a trustworthy company or organization to manipulate people into clicking on malicious links and provide sensitive information.
- Phishing is in the form of scam email or message delivered to many people at once, hoping to catch as many victims as possible.
Spear Phishing:
Spear phishing favors quality, meaning attempting to attack a specific victim with very personalized messaging.
- Spear phishing is like a targeted scam email or message and attackers do research on specific individuals or organizations to make their messages more convincing.
- They deliver messages in such a way that manipulate users into giving away sensitive information.
In a simple way, we can say phishing is aimed for many individuals, whereas spear phishing is aimed for a single individual or organization.
How to identify a spear phishing email:
To identify a spear phishing email, we should look for sender’s email address that doesn’t match the actual sender, subject lines are attractive or create a sense of urgency, a personalized salutation that uses your name or job title, generic content with spelling mistakes, and attachments or links from strangers. If you are not sure about the legitimacy of an email, it’s good to be cautious and avoid clicking on links or downloading attachments.
Safeguard Yourself Against Spear Phishing
Here are some preventative measures you may take to avoid spear phishing attacks.
- Use Anti-Phishing Software: Anti-phishing software can analyze phishing emails and avoid them from reaching your inbox. Algorithms are used in these programmes to analyze email messages and detect phishing signs such as fake attachments or links.
- Enable Two-Factor Authentication: 2-FA, gives an extra layer protection to your accounts. After entering password, it request for second form of verification i.e., multifactor authentication. This prevents attackers from gaining access to your accounts even if they find out your password.
- Keep Your Software Up to Date: Check your web browser, operating system and other applications to be up to date. This can help prevent attackers from exploiting vulnerabilities.
- Be Cautious of Links and Attachments: Email links and attachments from strangers should be avoided because it may contain malware. However, once check the actual URL and then compare it to the projected URL.
- Verify Requests for Sensitive Information: Be careful of emails or messages which are asking for sensitive information such as passwords or bank account details. Once check with the actual person in another communication channel if it is sent from actual person or not.
- Educate Yourself and Your Employees: Educate yourself and your employees on the perils of spear phishing and how to recognise and avoid them. This can help to prevent successful attacks and lessen damage if they do happen.
By taking these precautions, you may better defend yourself from spear phishing attempts and lower your chances of being a victim.
Conclusion:
spear phishing is a targeted form of cyberattack where attackers use personalized messages to deceive individuals or organizations into revealing sensitive information or performing harmful actions. Staying informed, being cautious, and employing proper security measures are essential in protecting against these types of attacks.