About XDR :
XDR (Extended Detection and Response) is a software as a service (SaaS) technology designed to provide detection and response solution based on the optimized security by fusing data and security products into straightforward solutions.
XDR broadens the definition of security in contrast to systems like endpoint detection and response (EDR), integrating protection across a wider variety of products. Organizations can use it to collect and correlate data across email applications, endpoints, cloud resources, servers, and networks. It enables teams to analyze, prioritize, hunt, and remediate threats for protection against data loss or breach. It offers a more effective, preventative solution as businesses increasingly deal with a changing threat landscape and difficult security issues involving workforces in multi-cloud, hybrid environments.
XDR Workflow :

NDR identifies suspected network activity and combine modern analytical methods that are not signature-based, such as machine learning. Teams may now respond to risks and abnormal or malicious communications that other security technologies might have missed.
EDR finds suspicious activity related to events from servers, mobile devices, laptops, desktop PCs, and even IoT and cloud workloads. To aid security operations analysts in identifying, analyzing, and resolving problems, they provide alerts.
The intension of the XDR workflow is to Visibility/transparency at multiple security levels (network, endpoint, applications), detection of known and unknown threats at a lateral level including all components, holistic monitoring and mitigation, vulnerability assessment, alerting and response, simplification and consolidation of events, and activities and targeted response.
Usefulness of XDR :
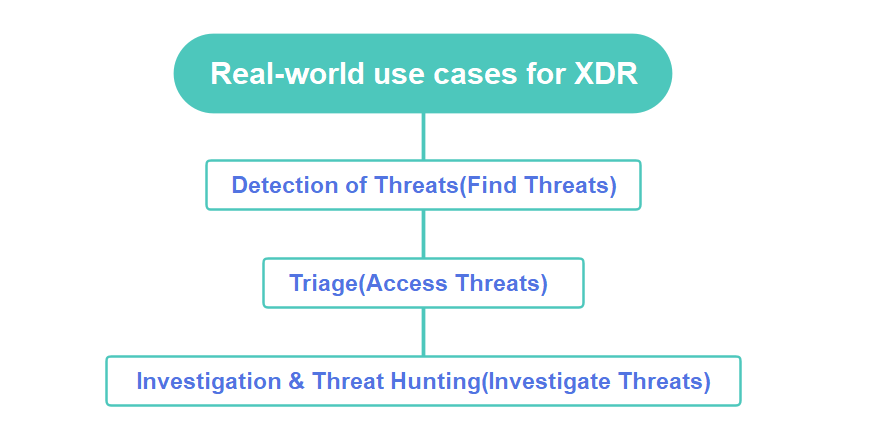
The Real-world use cases listed below are the key functions in the investigation of cybersecurity threat.
Threat Detection :
With the help of using artificial intelligence and machine learning, XDR is able to performs continuous threat detection and hunts hidden, stealthy and sophisticated threats proactively and quickly.
It spots threat that have been missed and alerts you to threats to get detected.
It helps to keep you safe and secured, even in cases where you’ve overlooked a key risk.
Triage :
Triage is another detection level which helps in flagging the severity and confidence level alerts. It is critical to assessing your systems and approach, alerting you when threats are coming your way, and prioritizing the way you handle these threats.
Investigation and Threat Hunting :
This is the core feature of the threats it helps to find where the threat origin from and what is the intension of that hunt and how to mitigate that threat.
It keeps tracks on threats across any source or location within the organization
XDR can easily get to the root of an incoming or past threat. XDR systems can keep reports of past incidents, too, so you can revisit an investigation at any time.
Benefits of XDR :

- It is cost efficient and holistic in nature. This is a major benefit of expanding their numbers of endpoints, collecting more data, and experimenting with hybrid work styles.
- Bu using out-of-the-box analytics and custom rules they detect advanced persistent threats and other covert attacks by monitoring 24/7 and also Protect network against insider abuse, external attacks, ransomware, fileless and memory-only attacks, and advanced zero-day malware.
- They provide endpoint protection by blocking known and unknown attacks from the known or unknown resources with integrated AI-driven antivirus and threat intelligence.
- They Simplify investigations with automated root cause analysis and a unified incident engine, reducing the number of alerts your team needs to review and lowering the skill required for triage.
- XDR enables the behavioral analytics on logs collected from third-party firewalls while integrating third-party alerts into a unified incident view and root cause analysis for faster investigations.
- They Root out adversaries by stopping attacks while avoiding user or system downtime.
- It restores and also recovers host from an attack by removing malicious files and registry keys, as well as restoring damaged files and registry keys using remediation suggestions.

XDR For Defending Critical Infrastructure :
By attempting to reduce complexity in their settings, critical infrastructure businesses can defend themselves from an assault. Security becomes more challenging as complexity increases. Thus, it is crucial to implement the appropriate security measures.
Deploying an XDR system is very advantageous for critical infrastructure organizations. It is a security strategy that extends the priorities of Endpoint Detection and Response (EDR) across endpoints, applications, cloud workloads, and other resources.
Some XDR platforms use threat intelligence to give security teams insight into what’s happening across all those environments, but the products are ineffective since they are pseudo-XDR solutions that are really just an EDR tool with a cloud integration.
Most of the EDR platforms are unable to even ingest all of the pertinent endpoint telemetry and are compelled to “filter out” intelligence even when they are unsure if that data is necessary for making a detection due to the solutions’ inability to handle the amounts of data collected.
These companies claim to be able to supply an XDR solution that ingests endpoint data in addition to a variety of telemetry from several other sources on the network and in the cloud, but they simply are unable to do so for their EDR.
Filtering out threat telemetry is not the best move when it comes to protecting critical infrastructure, or any network for that matter. More is always better when it comes to some things, and XDR is one of them.
Reference :
https://thehackernews.com/2022/12/how-xdr-helps-protect-critical.html
https://www.cybereason.com/blog/securing-critical-infrastructure-with-xdr
https://www.samurai.security.ntt/blog/xdr-benefits-cyberSecurity
https://www.stamus-networks.com/blog/xdr-extending-detection-and-response-with-ndr
For further clarifications or support, please write to contact@paradigmitcyber.com

