Proof-of-concept code for a vulnerability that may be remotely exploited through a WiFi connection to take control of iPhone 7 phones has been disclosed by a Google security researcher. A well-known vulnerability affecting the Wi-Fi chips used in some Apple iPhones was discovered in 2017. This vulnerability was known as “Broadpwn” (CVE-2017-11120).
About the Vulnerability:
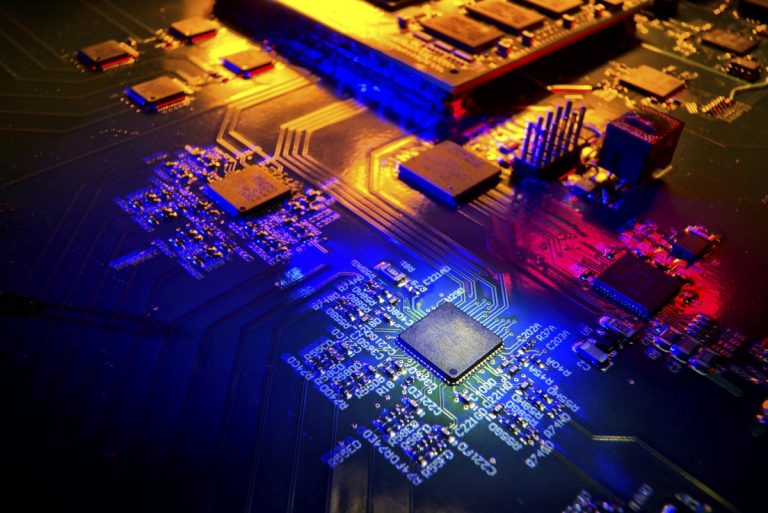
The Vulnerability allowed an attacker to send specially crafted Wi-Fi packets to the targeted device from anywhere inside the Wi-Fi network’s coverage area. After the exploit is successfully used, a backdoor is added to the firmware, enabling remote read/write commands to be sent to the firmware via specially constructed action frames, enabling simple remote control of the Wi-Fi chip. The Broadpwn hack took use of a flaw in Broadcom Wi-Fi chip firmware. A buffer overflow in the Wi-Fi chip’s firmware resulted from the vulnerability when a device with an affected Wi-Fi chip received particular malicious Wi-Fi packets.
By taking advantage of this buffer overflow, a hacker was able to take control of the impacted device. The attacker might run any code on the device without the need for user input or authentication by creating and sending specially crafted Wi-Fi packets. Once in charge, the attacker might be able to view and alter private information, put harmful software or malware on the device, and take unauthorised actions. The user and their data may be at serious risk of security with this level of access.
Features
- Remote Code Execution: The vulnerability enabled the execution of arbitrary code remotely, allowing an attacker to take control of a targeted device without the need for user input or authentication.
- Wi-Fi Range Exploitability: If an attacker is within the Wi-Fi network range of the targeted device, they may take advantage of the vulnerability. This implies that an attack could only be launched if the attacker was close in proximity to the gadget.
- Broadcom Wi-Fi Chipset Impact: The Broadcom BCM43xx series of Wi-Fi chips, which were widely utilised in numerous devices, including some iPhone models, were especially impacted by the vulnerability. The vulnerability was serious in terms of the potential impact and the number of impacted devices due to its widespread usage.
- Buffer Overflow Exploitation: A buffer overflow in the firmware of the Broadcom Wi-Fi chips was exploited. The attacker might take over the device by delivering specially designed Wi-Fi packets that would cause a buffer overflow.
- Device Compromise: If the flaw was successfully exploited, an attacker may take over the intended device. They were able to access and alter data, put malware on the infected device, and take unauthorised acts thanks to the amount of access they had.
- Vendor Response and Patching: Affected companies, including Apple, responded to the Broadpwn vulnerability by releasing security patches and firmware updates to fix the problem. The quick response and patching reduced the vulnerability’s potential impact.
Impact of the attack
- Device Compromise: The attack’s principal consequence is that the impacted devices may be insecure. The vulnerability could be used by an attacker to gain control of the system, giving them access to and control over data, the ability to install malware or spyware, and the capacity to perform illegal actions.
- Data Breach: If an attacker uses the Broadpwn method to take control of an iPhone, they might be able to access any stored sensitive data. Passwords, emails, contacts, messages, photos, and other private information may be included in this. Errors in sensitive data can lead to identity theft, financial loss, or other privacy-related issues.
- Unauthorised Tasks: Once an attacker has gained control of a compromised device, they can utilise it for a number of unauthorised activities. This could involve accessing restricted networks or systems, making unauthorised phone calls or text messages, sending spam or phishing emails, or even launching subsequent attacks on other devices or networks.
- Malware Installation: The hacker may use the infected iPhone to install malware or spyware, enabling them to secretly gather private information, keep track of the user’s activities over time, or perform other criminal activities.
- Privacy Breach: The compromise of the Wi-Fi chip poses a threat to user privacy. If hackers get access to users’ personal data, chats, or other sensitive information, their right to privacy may be violated.
Mitigation
As soon as the flaw was identified, Apple and Google (as it also affected some Android devices) collaborated to create security updates. In order to remedy the problem, Apple released iOS 10.3.3, which fixed the Broadpwn vulnerability. To safeguard their phones against potential exploits, users were strongly advised to update their iPhones to the most recent firmware.
- Update your device: Make sure your iPhone is running the most recent version of its operating system or firmware. With the release of iOS 10.3.3, Apple fixed the Broadpwn vulnerability. Your device will be patched and protected against potential exploits if you update it to the most recent firmware.
- Enable automatic updates: This will ensure that your device continues to be protected from known vulnerabilities. In this way, as soon as Apple releases new security fixes and firmware updates, your device will get them.
- Avoid untrusted networks: When using public Wi-Fi, especially in new or untrusted locations, use caution. To increase security, utilise a trusted virtual private network (VPN) or limit your use of public Wi-Fi networks.
- Use cellular data when possible: If you find yourself in a scenario where you can’t rely on the Wi-Fi network, you might want to use your cellular data connection instead. By doing this, the risk of potential Wi-Fi-based attacks is decreased.
- Exercise caution with Wi-Fi usage: Make sure the Wi-Fi networks you connect to are from reliable sources and be careful the ones you connect to. Avoid from connecting to open or unsecured networks that might be attacked.
- Regularly create device backups: Make regular iPhone backups to ensure that your data is secure in the event of a loss or compromise. In this manner, if necessary, you can quickly restore your data.
Reference:
https://thehackernews.com/2020/12/google-hacker-details-zero-click.html
https://threatpost.com/remote-wi-fi-attack-backdoors-iphone-7/128163/
For further clarifications or support, please write to contact@paradigmitcyber.com