Introduction:
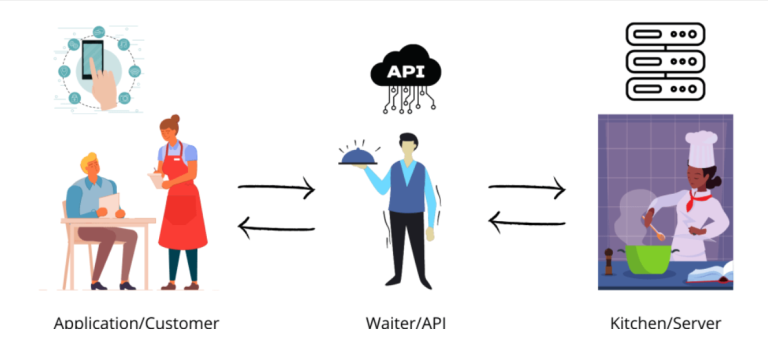
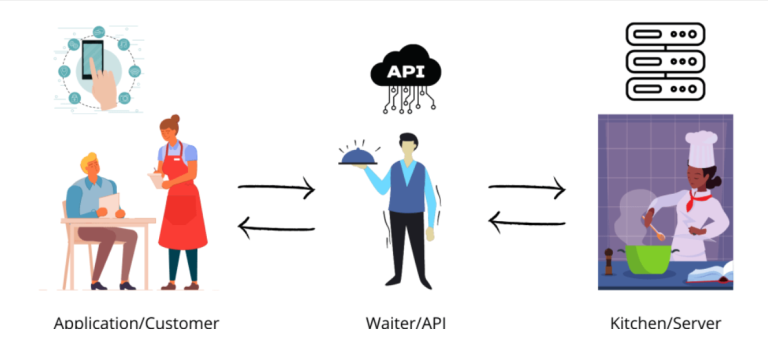
Modern computer approaches must now include Application Programming Interfaces (APIs), which make it simple to share contacts and data. Nevertheless, a variety of security concerns put them in danger. This post will address the top 10 API risks that put apps at risk in addition to mitigating measures for strengthening API security.
1. Attacks based on injection:
Injection attacks, such as SQL injection and NoSQL injection, occur when an attacker inserts malicious code into API parameters or data fields. To ensure that user-supplied data is treated as data and not executable code to thwart injection attempts, implement input validation and parameterized queries.
2.Broken session management and authentication:
The mechanisms for session management and authentication are vulnerable to this attack. Attackers could steal user data, pose as someone else, or hijack active sessions. Use secure authentication processes, enforce rigorous session management standards, and regularly validate session tokens to thwart such attacks.
3. XSS (Cross-Site Scripting):
Cross-Site Scripting involves injecting malicious scripts into API answers, which are subsequently carried out by users’ browsers.
4. Cross-Site Request Forgery (CSRF):
CSRF attacks trick authorized users into performing unlawful deeds. To stop CSRF attacks, use anti-CSRF tokens, secure HTTP verbs, and double-check the Referrer header.
5. XML External Entity (XXE) Attacks:
XXE attacks use shoddy XML parsers to read arbitrary files, run remote code, or launch denial-of-service attacks. Disable external entity resolution, validate and sanitize XML input, and use secure XML parsers to protect against XXE assaults.
6.Man-in-the-Middle (MitM) Attacks:
A MitM attack is when an attacker intercepts and alters data being transmitted between API clients and servers. By employing HTTPS/TLS secure communication routes, checking server certificates, and encrypting data, MitM attacks can be reduced.
7. Attacks, such as Distributed Denial-of-Service and Denial-of-Service:
DoS and DDoS attacks aim to overwhelm API servers and bring them to a halt. To identify and halt DoS and DDoS assaults, use rate limitation, request throttling, and traffic monitoring technologies.
8. Large-scale Assignment:
The usage of APIs by attacks like “mass assignment” might result in data tampering or unauthorized access since they permit extensive data change. Apply input verification, the least privilege principle, and appropriate access constraints to lessen the risks associated with bulk assignment.
9. Ineffective Error Handling:
Inadequate error handling can provide attackers access to private data about the API, how it was implemented, or the underlying systems. Provide generic error messages to users, log detailed errors only for debugging purposes, and ensure sensitive information is not exposed.
10. Insecure Direct Object References:
When a perpetrator tampers with object references in API requests to access restricted resources or alter data, the result is an IDOR attack. Use secure authentication and authorization mechanisms, unique IDs, and access privilege checks before authorizing any requests to prevent IDOR attacks.
Conclusion:
To shield apps and their users from numerous assaults, API security is crucial. Developers and security teams may improve the security posture of their APIs and protect sensitive data by identifying and mitigating the top 10 API vulnerabilities, which include injection attacks, flawed authentication, XSS, CSRF, XXE, MitM, DoS/DDoS, bulk assignment, incorrect error handling, and IDOR. It’s critical to do regular security assessments, examine your code often, and keep up with the most recent security best practices. Regular security assessments, code reviews, and staying updated with the latest security best practices are vital to maintain robust API security.
References:
https://apisecurity.io/encyclopedia/content/owasp/owasp-api-security-top-10.htm https://curity.io/resources/learn/owasp-top-ten/ For further clarifications or support, please write to contact@paradigmitcyber.com