Introduction:
In the world of web development and application programming interfaces (APIs), security is a paramount concern. As APIs become increasingly prevalent, it is crucial to ensure that they are protected against potential vulnerabilities. Enter Postman, a widely used and versatile tool that not only assists in API development but also serves as an asset for API penetration testing. In this blog post, we will explore the installation process, delve into the features of Postman, and understand how it can be utilized for effective API penetration testing. 
Installing Postman:
- Download: Visit the official Postman website at https://www.postman.com/downloads/ and download the version compatible with your operating system (Windows, macOS, or Linux).
- Installation: Once the download is complete, run the installer and follow the instructions provided.
- Account Creation: Postman requires a user account to access its features fully. Sign up for an account if you don’t already have one.
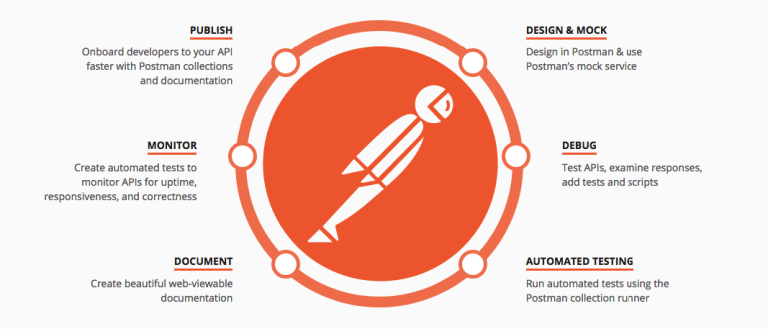
Key Features of Postman:
- Request Building: Postman provides a user-friendly interface for building API requests, enabling developers and testers to define parameters, headers, authentication details, and more.
- Collections and Environments: Organize API requests into collections and create different environments to streamline the testing process across various scenarios.
- Testing and Automation: Leverage the built-in testing framework in Postman to validate API responses, perform assertions, and automate repetitive tasks.
- Collaboration and Sharing: Share collections with team members, collaborate on testing efforts, and streamline workflows by leveraging Postman’s team features.
- Mock Servers: Simulate API responses by creating mock servers in Postman, allowing testing even before the actual backend implementation is complete.
- Documentation: Generate comprehensive API documentation using Postman’s tools, making it easier for developers to understand and utilize your APIs.
Utilizing Postman for API Penetration Testing:
- API Discovery: Identify the target APIs and endpoints to test for potential vulnerabilities.
- Authorization and Authentication: Configure Postman to handle various authentication methods (such as JWT, OAuth, or Basic Auth) and explore authorization-related security flaws.
- Input Validation: Test the API by injecting invalid, unexpected, or excessively large inputs to uncover vulnerabilities like input validation errors and potential buffer overflow issues.
- Injection Attacks: Attempt injection attacks, such as SQL injection or OS command injection, to identify potential security weaknesses.
- Access Control: Test the API’s access control mechanisms to ensure they effectively restrict unauthorized access to sensitive data or functionality.
- Error Handling: Evaluate the API’s error handling capabilities by manipulating requests to trigger unexpected errors and assess the level of detail exposed in error responses.
- SSL/TLS Implementation: Inspect how the API handles SSL/TLS connections and verify the correct implementation of certificates and encryption protocols.
- Performance and Load Testing: Utilize Postman’s capabilities to simulate high loads and stress test the API for potential performance and security concerns.
Conclusion:
Postman proves to be an invaluable tool for API penetration testing, empowering developers, and security testers to identify and mitigate potential vulnerabilities. With its comprehensive features, user-friendly interface, and robust testing capabilities, Postman streamlines the process of ensuring the security and reliability of APIs. By implementing rigorous testing practices and leveraging Postman’s capabilities, organizations can bolster their API security posture and protect against potential threats in an ever-evolving digital landscape.
Citations:
https://www.postman.com/api-platform/api-testing/ https://www.optiv.com/insights/discover/blog/getting-started-postman-api-security-testing-part-2 https://www.testdevlab.com/blog/using-postman-for-api-testing
For further clarifications or support, please write to contact@paradigmitcyber.com