
- Cyber Security, Social engineering attacks



Threats, Trends and Technologies on the Rise Over the

Pocket-size Devices don’t mean Pocket Size Threats In contemporary


Unveiling the Complexities of IoT Security Interconnected ecosystems have

How to choose the right Third-Party partner for your

How to protect yourself against the timeless cyberattack? Rapid

The saying “The road to hell is paved with

In a rapidly evolving landscape of digital threats, the

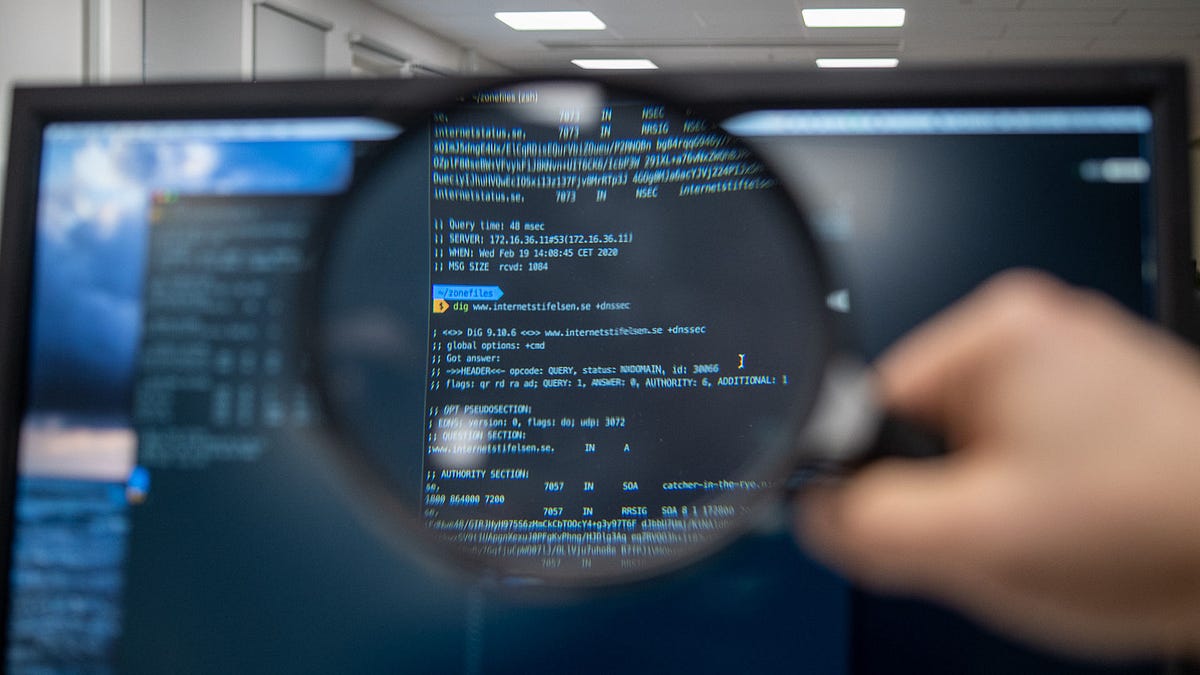
The security researcher and investigators have found an open

Being a member of the cybersecurity sector means
EXECUTIVE SUMMARY : At the face of an ever-evolving
Introduction: Organizations face a variety of hazards in
In today’s interconnected digital landscape, APIs (Application Programming
The key to personalization and control is jailbreaking,

Introduction: For web applications to be secure and

Introduction: In the world of software development and

Introduction: API security is a vital component of
© 2025 ParadigmIT Cybersecurity. All Rights Reserved.